Tracer FIRE
Abstract
Tracer FIRE (Forensic and Incident Response Exercise) for the U.S. Department of Energy (DOE) is a program developed by Sandia National Laboratories to educate and train cyber security incident responders (CSIRs) and analysts in critical skill areas. The program also aims to improve collaboration and teamwork among staff members. Under this program, several hundred CSIRs from the DOE, other U.S. government agencies, and critical infrastructure organizations have been trained.
Tracer FIRE 11's scenario involves multiple cyber-attacks on the fictional water company Orko. Orko Water Authority manages IT and ICS devices to provide water for the state. Attackers have infiltrated these systems causing disruptions to multiple Orko services. Participants will investigate these attacks using open- source hunting tools and determine exactly what occurred and make recommendations to the oversight board on how to remediate/recover from these attacks.
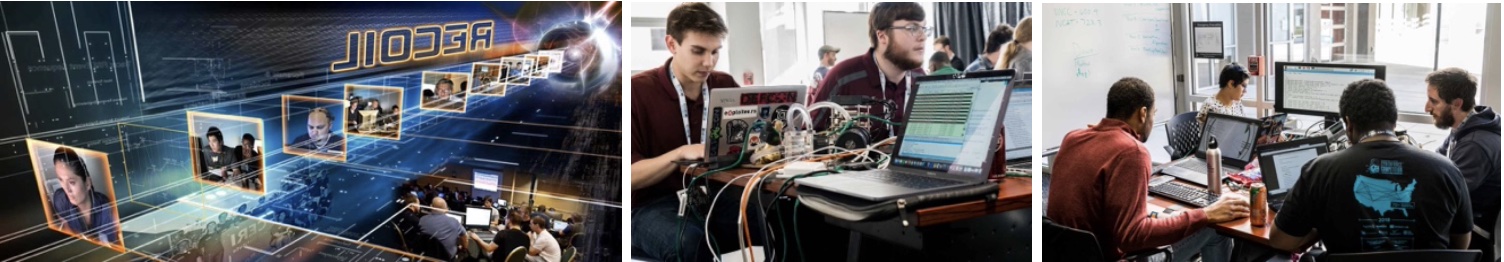
This is the eleventh Tracer FIRE to be offered at ACSAC. Discussion topics in the workshop include incident response, forensic investigation, and live analysis on file system, memory, and malware. Attendees will be introduced to a number of forensic tools and techniques that can be used to solve forensic challenges on the second half of the workshop. Attendees will be able to:
- Familiarize themselves with the Cyber Kill Chain
- Perform forensic analysis on infected machines and memory images via Velociraptor and Volatility
- Analyze traffic on how malware communicates over its command and control (C2) using Arkime and Elastic
- Reverse Engineer malicious binaries using Ghidra
- Utilize a SIEM (Security Information and Event Management) and IDS (Intrusion Detection System).
Outline
Day 1:
- Introduction and demo of the tools (7 hours)
- Begin the competition (remainder of the day)
Day 2:
- Continue the competition
- Final Debrief and awards (last hour)
Prerequisites
Attendees will require a basic understanding of computer systems, networks and general cyber security concepts.
Student Equipment requirements:
Laptop with network access.
Instructors
Kevin Nauer is a member of the technical staff at Sandia and has over 20 years of experience in researching malware and conducting digital forensic analysis. Recently, he has been leading a team of security practitioners to develop engaging scenarios that are used in various capture the flag type of exercises for universities and government agencies. Kevin holds a B.S. and M.S. in Computer Science and has previously served as a Captain in the US Army Intelligence and Security Command where he helped to lead a new organization to conduct digital media exploitation.
Kelcey Tietjen has been an active incident responder and forensicator since 2004. Kelcey has built, managed, or worked in incident response capabilities at Mandiant, Apple, Bechtel, and Los Alamos National Laboratory. He currently is focused on cloud incident response and forensics in a cybersecurity research group at Sandia National Laboratories.
Tyler Morris is a senior security researcher at Sandia National Laboratories. At Sandia Tyler works on developing future cybersecurity technologies in areas of deception, forensics, software, and security scenarios like Tracer FIRE.